Top Cyber Security Challenges Businesses Will Face in 2026 — A Complete Guide
The Cyber Security landscape is evolving at a pace never seen before. As businesses move deeper into cloud adoption, automation, digitization, and AI-driven operations, their exposure to cyber threats continues to grow. Unfortunately, cybercriminals are also evolving—leveraging advanced tools, automation, and artificial intelligence to launch attacks that are more sophisticated and more damaging.
By 2026, organizations across all industries will face a combination of new, emerging threats along with intensified versions of older ones. This makes Cyber Security not just an IT requirement but a fundamental pillar of business continuity, compliance, and customer trust. This blog explores the biggest Cyber Security challenges businesses must prepare for in 2026, along with detailed explanations of how each threat impacts modern digital environments.
Why Cyber Security Matters More in 2026
Businesses today operate in a hyperconnected world—cloud platforms, remote teams, mobile devices, smart IoT systems, and AI-powered tools form the backbone of daily operations. While this digital expansion creates efficiency and innovation, it also widens the attack surface dramatically.
In 2026, companies must adopt Cyber Security practices that are proactive, automated, intelligence-driven, and capable of protecting distributed environments. Without strong Cyber Security frameworks, organizations risk financial loss, service downtime, data exposure, compliance penalties, and reputational damage that could take years to repair.
AI-Powered Cyber Attacks Will Become the Biggest Threat
Artificial intelligence is changing everything—including the way cybercriminals operate. Attackers now use AI to automate phishing, scan networks, exploit vulnerabilities, and bypass traditional security controls.
How AI-Powered Attacks Work
AI enables threat actors to:
Generate highly convincing phishing emails and messages personalized for each target
Create deepfake voice and video to impersonate employees or executives
Build malware that adapts itself to avoid detection
Automatically scan cloud environments for misconfigurations
Use machine learning to guess passwords or bypass authentication systems
As attackers adopt AI-driven automation, traditional detection systems become less effective. Businesses must integrate AI-based Cyber Security solutions that monitor behavior patterns, detect anomalies instantly, and respond in real time.
Impact on Businesses
AI-powered attacks lead to faster breaches, large-scale data theft, and extremely targeted social engineering attempts. Without advanced Cyber Security tools, companies can be compromised in minutes.
Ransomware Will Become More Aggressive and Complex
Ransomware has been one of the most damaging Cyber Security threats for the past decade, and in 2026, it will only get worse. Attackers are shifting from simple file encryption toward multi-step extortion strategies that place tremendous pressure on victims.
New Ransomware Trends in 2026
Double extortion: Attackers steal data before encrypting it and threaten to leak it publicly.
Triple extortion: Hackers attack the victim’s customers, vendors, or partners to multiply the pressure.
Ransomware-as-a-Service (RaaS): Criminal groups sell ready-made ransomware kits to amateur hackers.
AI-driven ransomware: Automated malware spreads faster and adapts to the environment.
Impact on Businesses
Ransomware can shut down operations, corrupt backups, leak sensitive data, and cause legal penalties. The recovery process can take weeks or months. Strengthening Cyber Security incident response and backup strategies will be essential to survive these attacks.
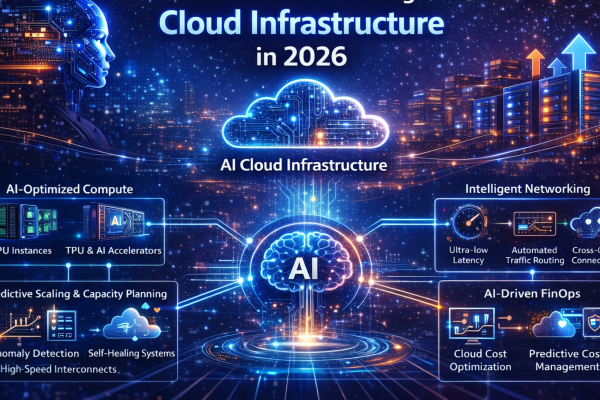
Cloud Misconfigurations Will Continue to Cause Major Breaches
As businesses expand into multi-cloud environments such as AWS, Azure, and Google Cloud, cloud misconfigurations remain one of the top causes of breaches. Even a small error—like leaving storage public or applying overly permissive IAM roles—can expose critical data.
Common Cloud Configuration Risks
Publicly accessible storage buckets
Weak or unused access keys
Over-permissive roles and policies
Exposed serverless functions
Misconfigured firewalls and security groups
Unsecured APIs
Why This Will Continue in 2026
Modern cloud architectures—including Kubernetes, serverless platforms, and distributed microservices—are complex. Manual configuration and monitoring are nearly impossible at scale. Businesses need automated cloud Cyber Security posture management (CSPM) tools to avoid critical misconfigurations.
Software Supply Chain Attacks Will Explode
Businesses depend heavily on third-party software, open-source libraries, and CI/CD pipelines. Unfortunately, attackers know this too—and they increasingly target software suppliers instead of the businesses themselves.
How Supply Chain Attacks Work
Attackers insert malicious code into open-source libraries
Hackers compromise CI/CD pipelines to push infected updates
Threat actors target developers using fake packages or malware
Vulnerabilities in build tools spread across thousands of apps
High-Profile Incidents Have Already Created Awareness
Events like SolarWinds and widespread NPM/PyPI poisoning campaigns show how dangerous supply chain attacks can be. In 2026, every business must adopt strong Cyber Security supply chain safeguards, including strict dependency checks, code signing, and secure DevOps practices.
Insider Threats Will Become More Frequent
Insider threats—whether intentional or accidental—will grow significantly as more employees work remotely, handle sensitive data, and use personal devices for work.
Types of Insider Threats
Accidental insiders who leak data through misconfiguration or negligence.
Compromised insiders whose accounts are taken over by attackers.
Malicious insiders who exploit their access for personal gain.
Why Insider Threats Are Increasing
- Remote work expands access outside corporate networks
- More employees use cloud apps and personal devices
- Human error continues to be the top cause of breaches
- Attackers use AI to trick employees into giving up credentials
Modern Cyber Security strategies must include Zero Trust architecture, continuous access monitoring, and behavioral analytics.
Identity Theft and MFA Bypass Attacks Will Rise
Identity is the new security perimeter. In 2026, attackers will increasingly target login credentials and authentication tokens instead of trying to break technical defenses.
MFA Bypass Techniques on the Rise
- Push notification spamming
- Deepfake voice calls for account resets
- SIM-swapping attacks
- Token theft through browser-in-the-browser attacks
- Fake authentication pages powered by AI
Why It Matters
Even if a business implements strong Cyber Security practices, compromised credentials can instantly give attackers access to critical systems. Organizations must adopt phishing-resistant authentication methods like FIDO2, hardware keys, and continuous identity risk scoring.
IoT and OT Devices Will Create Massive Security Gaps
IoT (Internet of Things) and OT (Operational Technology) devices are rapidly expanding in industries like healthcare, manufacturing, retail, logistics, and smart cities. Unfortunately, they often lack strong security features.
Common IoT/OT Security Issues
Outdated firmware
Hard-coded passwords
Weak or no encryption
Direct internet exposure
Lack of logging and monitoring
Cyber Security Impact
A single compromised IoT sensor can become the entry point for attackers to move laterally across a network, disrupt operations, or steal data. Businesses must implement device segmentation and continuous monitoring to defend against IoT-based attacks.
Quantum Computing Threats Will Begin to Emerge
Quantum computing is not yet mainstream—but by 2026, progress will force businesses to rethink their encryption strategies. Quantum algorithms may become capable of breaking traditional encryption systems like RSA and ECC.
What This Means for Businesses
Organizations must prepare for the transition to post-quantum cryptography. Sensitive data stored today may be decrypted in the future once quantum systems mature. Future-proofing Cyber Security involves adopting encryption that is resistant to quantum threats.
API Attacks Will Increase Due to Microservices and SaaS Growth
APIs now power mobile apps, SaaS platforms, microservices, and automated workflows. Attackers recognize this—and they increasingly target APIs to steal data, bypass authentication, or disrupt services.
Common API Security Issues
- Unprotected endpoints
- Broken authentication
- Data overexposure
- Weak access controls
- Lack of rate limiting
API Cyber Security is becoming one of the most important areas for businesses to improve as APIs become the backbone of digital systems.
Lack of Continuous Monitoring and Slow Response Will Cause Damage
Cyber attacks today are fast. Many can compromise a system in seconds and extract data within minutes. Yet most businesses still rely on security tools that detect threats too late.
Why Continuous Monitoring Matters
- Real-time detection prevents widespread damage
- Early alerts reduce downtime
- Automated responses help stop attacks instantly
Organizations must invest in Security Operations Centers (SOC), SIEM tools, SOAR platforms, and AI-driven alert systems to strengthen their Cyber Security posture.
Conclusion
As we move into 2026, businesses must understand that Cyber Security Services is no longer a secondary IT function—it is the backbone of trust, continuity, and digital growth. With threats becoming more intelligent, automated, and complex, companies must adopt modern security frameworks that emphasize Zero Trust, AI-powered defenses, cloud security automation, identity protection, and continuous monitoring.
Organizations that invest in these technologies and strategies will be far better equipped to handle the evolving threat landscape. Those that ignore them risk downtime, financial loss, data exposure, reputation damage, and legal penalties that can jeopardize long-term success.
Strong Cyber Security is not just protection—it is a competitive advantage.
Author